|
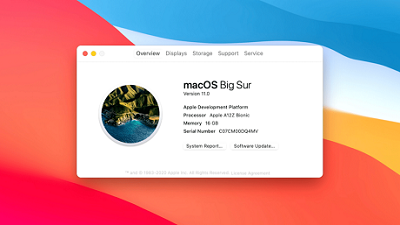
America’s former top trade negotiator Charlene Barshefsky said the Donald Trump administration had “no policy” on China. Perhaps the most obvious example has been its overtly hostile but ultimately directionless assault on mainland 5G pioneer Huawei. The US government has used cyberspying, hacking, “lawfare”, diplomacy and disinformation – just about every possible tactic – to discredit and undermine the telecoms company. Yet, in the latest twist to this long-standing saga, it will reverse a ban on US firms from working with Huawei to develop 5G infrastructure and protocols. The reversal comes after top US tech giants complained they had no choice but to work with the blacklisted Chinese company because the latter holds many key patents and has been integral to the development of 5G standard protocols. Such development has been in the works for many years, involving top global companies and many government agencies under the auspices of the 3rd Generation Partnership Project (3GPP), an international collaboration of seven telecoms standard development organizations responsible for evolving mobile system specifications. Conspicuously, agencies of the United States government have been absent from many of those key gatherings where international standards are developed and adopted. But Beijing, Huawei, and other Chinese tech companies have been among the most active participants, resulting in the leading role they now play. Since Trump took office, his administration realized too late that the US has lagged far behind in 5G. Its hostile strategy to undermine Huawei and other Chinese firms may at first make sense. But Huawei is too entrenched in the game to be just kicked out of it on the say-so of Uncle Sam. China’s road to 5G was the industrial policy at its most spectacular. In 2012, two years before China Mobile launched 4G services on the mainland, Chinese companies joined international initiatives such as 3GPP to research and develop 5G infrastructure. Today, the country accounts for 35 percent of 5G standard-essential patents. Of these, about 15 percent are owned by Huawei. By comparison, the share of US firms is estimated at about 13 percent. US officials should realize they are hurting their own industry and companies by blocking and punishing Huawei. Even if they manage to force some of its key allies to exclude the Chinese telecoms giant from their 5G projects, they will end up suffering delays and having to pay Huawei in terms of royalties. In light of the latest rule reversal and constructive meetings between the two countries’ top diplomats, it is time for both sides to reach an understanding to enable all hi-tech companies to compete fairly and reap the rewards of their pioneering efforts. Follow these developments and more on OUR FORUM. On May 6, 2002, Steve Jobs opened WWDC with a funeral for Classic Mac OS, 18 years later, OS X finally reached its own end of the road: the next version of macOS is not 10.16, but 11.0. OS X has one of the most fascinating family trees in technology; to understand its significance requires understanding each of its forebearers. Unix does refer to a specific operating system that originated in AT&T’s Bell Labs (the copyrights of which are owned by Novell), but thanks to a settlement with the U.S. government (that was widely criticized for going easy on the telecoms giant), Unix was widely-licensed to universities in particular. One of the most popular variants that resulted was the Berkeley Software Distribution (BSD), developed at the University of California, Berkeley. Today you can still run nearly any Unix program on macOS, but particularly with some of the security changes made in Catalina, you are liable to run into permissions issues, particularly when it comes to seamlessly link programs together. Mach was a microkernel developed at Carnegie Mellon University; the concept of a microkernel is to run the smallest amount of software necessary for the core functionality of an operating system in the most privileged mode and put all other functionality into less privileged modes. OS X doesn’t have a true microkernel — the BSD subsystem runs in the same privileged mode, for performance reasons — but the modular structure of a microkernel-type design makes it easier to port to different processor architectures, or remove operating system functionality that is not needed for different types of devices (there is, of course, lots of other work that goes into a porting a modern operating system; this is a dramatic simplification). The story of Steve Jobs’ visiting Xerox is as mistaken as it is well-known; the Xerox Alto and its groundbreaking mouse-driven graphical user interface were well-known around Silicon Valley, thanks to the thousands of demos the Palo Alto Research Center (PARC) did and the papers it had published. PARC’s problem is that Xerox cared more about making money from copy machines than in figuring out how to bring the Alto to market. That doesn’t change just how much of an inspiration the Alto was to Jobs in particular: after the visit, he pushed the Lisa computer to have a graphical user interface, and it was why he took over the Macintosh project, determined to make an inexpensive computer that was far easier to use than anything that had come before it. The Macintosh was not the first Apple computer: that was the Apple I, and then the iconic Apple II. What made the Apple II unique was its explicit focus on consumers, not businesses; interestingly, what made the Apple II successful was VisiCalc, the first spreadsheet application, which is to say that the Apple II sold primarily to businesses. Still, the truth is that Apple has been a consumer company from the very beginning. This is why the Mac is best thought of as the child of Apple and Xerox: Apple understood consumers and wanted to sell products to them, and Xerox provided the inspiration for what those products should look like. It was NeXTSTEP, meanwhile, that was the child of Unix and Mach: an extremely modular design, from its own architecture to its focus on object-oriented programming and its inclusion of different “kits” that were easy to fit together to create new programs. If one were to add iOS to the family tree I illustrated above, most would put it under Mac OS X; I think, though, iOS is best understood as another child of Classic Mac and NeXT, but this time the resemblance is to the Apple side of the family. For the complete story stop by OUR FORUM.
The Evil Corp group, also known as the Dridex gang, has been active since 2007 when several members previously involved with the ZeuS banking trojan decided to try their own luck at distributing malware. Ther initial efforts were focused on distributing the Cridex banking trojan, a malware strain that later evolved into the Dridex banking trojan, and later subsequently evolved into the Dridex multi-purpose malware toolkit. Across the years, Evil Corp, through its Dridex operation became one of the largest malware and spam botnets on the internet. The group distributed their own malware, but also malware for other criminal groups, along with custom spam messaging. The group dipped their toes into ransomware distribution by spreading the Locky ransomware to home consumers throughout 2016. As the ransomware market began shifting targeting from home consumers to enterprise targets, the Evil Corp gang adapted as well, and after dropping the Locky strain for good, they created new custom ransomware named BitPaymer. The group used their vast botnet of computers infected with the Dridex malware to look for corporate networks and then deploy BitPaymer on the largest enterprise targets they could identify. The group operated BitPaymer between 2017 and 2019 when new infections started dropping off. The reasons are unclear, but the slowdown in BitPaymer infections may have also had something to do with the Dridex botnet slowing down its activity between 2017 and 2019. Fox-IT says that this slowdown culminated with the DOJ charges filed in December 2019. Following the high-profile indictments, the group went silent for a full month until January 2020. According to Fox-IT, the group came back to life in January and spurted a few malware campaigns, usually for other crooks, until March, when they again went silent. However, when the group returned to life for the second time in 2020, they did so with new tools. Fox-IT says the group created a new ransomware strain to replace the aging BitPaymer variant that they've been using since early 2017. The actual reasons for replacing BitPaymer are shrouded in mystery; however, Fox-IT, says this replacement appears to be a totally new ransomware strain, written from scratch. Fox-IT says it named this new ransomware WastedLocker based on the file extension it adds to encrypted files, usually consisting of the victim's name and the string "wasted." Security researchers say that an analysis of this new ransomware has revealed little code reuse or code similarities between BitPaymer and WastedLocker; however, some similarities still remain in the ransom note text. In an interview with ZDNet earlier today, Fox-IT says they've been tracking the use of this new ransomware family since May 2020. They say the ransomware has been exclusively deployed against US companies. "Ransom demands that are asked by Evil Corp are now typically into the millions," Maarten van Dantzig, Fox-IT security researcher, told ZDNet today. Want to know more please visit OUR FORUM. |
Latest Articles
|